EC-Council’s CCISO Program has certified leading information security professionals around the world.
A core group of high- level information security executives, the CCISO Advisory Board, contributed by forming the foundation of the program and outlining the content that would be covered by the exam, body of knowledge, and training.
Some members of the Board contributed as authors, others as exam writers, others as quality assurance checks, and still others as trainers. Each segment of the program was developed with the aspiring CISO in mind and looks to transfer the knowledge of seasoned professionals to the next generation in the areas that are most critical in the development and maintenance of a successful information security program.
The Certified CISO (CCISO) program is the first of its kind training and certification program aimed at producing top-level information security executives. The CCISO does not focus solely on technical knowledge but on the application of information security management principles from an executive management point of view. The program was developed by sitting CISOs for current and aspiring CISOs.
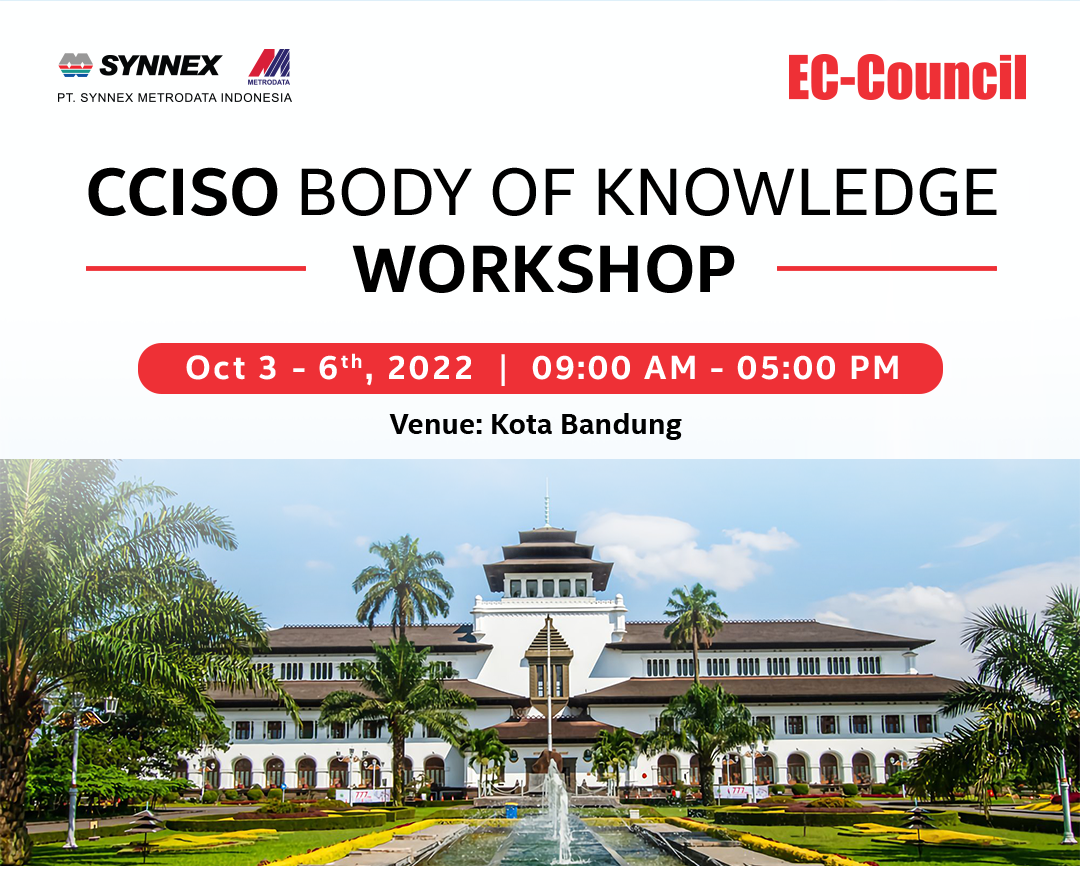
Schedule : Oct 3-6th, 2022
Venue : InterContinental Hotel Dago Pakar Bandung, Jalan Resor Dago Pakar Raya 2B Resor Dago Pakar, Kota Bandung, Jawa Barat
Time : 09:00 AM – 05:00 PM
Official Trainer :
 Mr. Faisal Yahya
Mr. Faisal Yahya
CCISO Official Instructor
Target Audience

Agenda :
Domain 1 : Governance and Risk Management
Domain 2 : Information Security Controls, Compliance and Audit Management
Domain 3 : Security Program Management and Operations
Domain 4 : Information Security Core Competencies
Domain 5 : Strategic Planning, Finance, Procurement and Vendor Management
Learn more about EC-Council CCISO Program
https://www.youtube.com/watch?v=mdoMRJsWKUU
More Information, contact us :
Elfini Violin | M: 0812-8511-7342 | E: elfini.violin@metrodata.co.id


